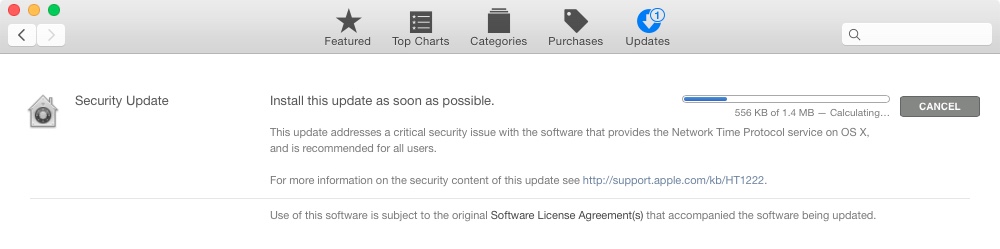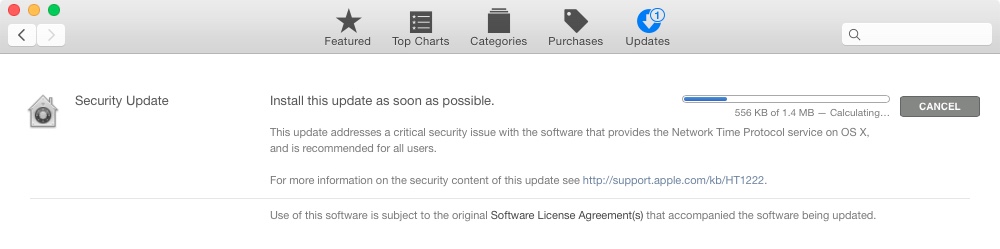
Apple issues OS X NTP Security Update for Mountain Lion, Mavericks and Yosemite.
OS X NTP Security Update
ntpd
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, OS X Yosemite v10.10.1
Impact: A remote attacker may be able to execute arbitrary code
Description: Several issues existed in ntpd that would have allowed an attacker to trigger buffer overflows. These issues were addressed through improved error checking.
To verify the ntpd version, type the following command in Terminal: what /usr/sbin/ntpd. This update includes the following versions:
Mountain Lion: ntp-77.1.1
Mavericks: ntp-88.1.1
Yosemite: ntp-92.5.1
CVE-ID
CVE-2014-9295 : Stephen Roettger of the Google Security Team
From ICS-CERT:
Google Security Team researchers Neel Mehta and Stephen Roettger have coordinated multiple vulnerabilities with CERT/CC concerning the Network Time Protocol (NTP). As NTP is widely used within operational Industrial Control Systems deployments, NCCIC/ICS-CERT is providing this information for US Critical Infrastructure asset owners and operators for awareness and to identify mitigations for affected devices. ICS-CERT may release updates as additional information becomes available.
These vulnerabilities could be exploited remotely. Exploits that target these vulnerabilities are publicly available.
Products using NTP service prior to NTP-4.2.8 are affected. No specific vendor is specified because this is an open source protocol.